Strategy access rights are defined by roles which are set for users/teams in each strategy part's settings. These roles define what each user can see, add, edit, publish or delete in each strategy and their parts. Let's start by reviewing the different roles with the help of a couple of informational charts. A complete description of each role can be found at the end of this article.
Strategy access rights visualized
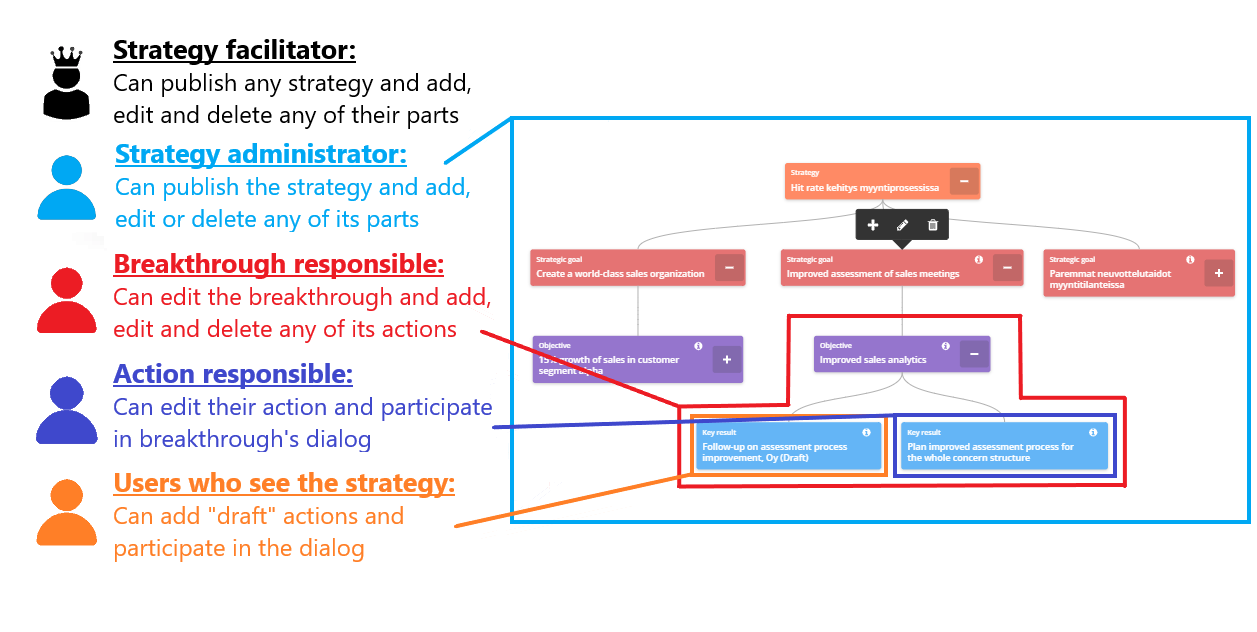
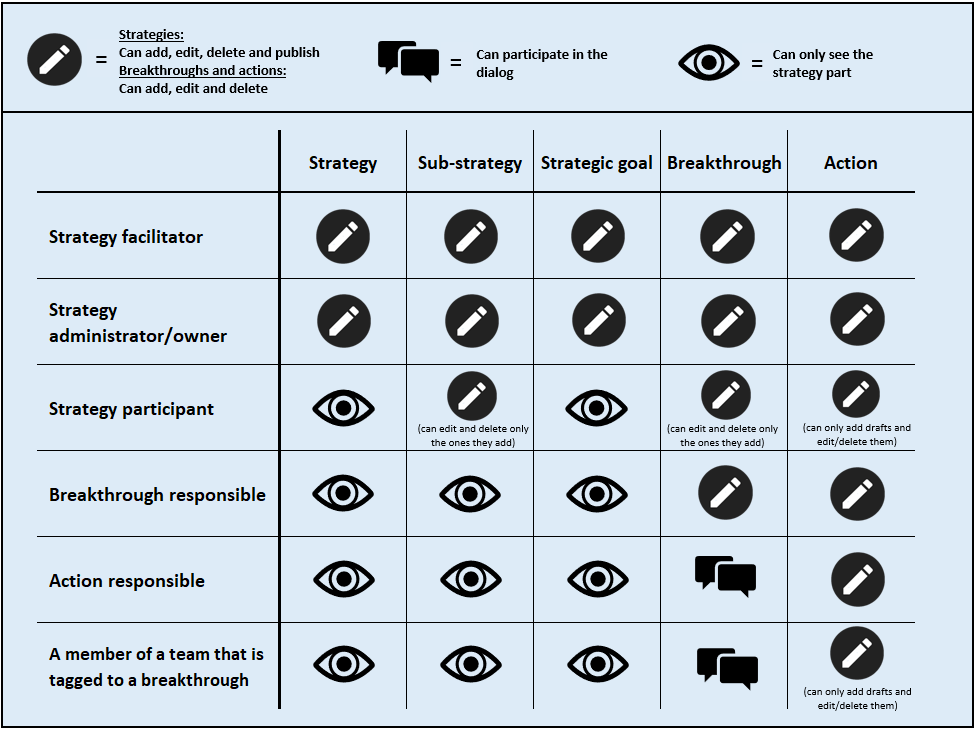
The chart above shows what each role can publish, add, edit or delete in a strategy. It's worth noticing that each of these roles can see all the parts of this strategy, but the add/edit/delete rights vary for each role:
- Strategy facilitators can publish any of the organization's strategies and add, edit and delete all strategy parts in strategies.
- Strategy administrators can publish the strategies they administrate and add, edit and delete all strategy parts in these strategies. In other words, administrators have the ability to publish and change everything in a strategy similar to facilitators, but only in the strategies they are separately set as administrators.
- Breakthrough responsibles can add, edit and delete their own breakthrough and its actions. As they can also see the other strategy parts, they won't have to do their strategy work detached from the rest of the organization.
- Action responsibles can edit their action and participate in the breakthrough's dialog. Similar to breakthrough responsibles, they can see the other strategy parts.
- If a user isn't defined as responsible, administrator or facilitator, but they nevertheless are able to see the strategy, they can only add "draft" actions and participate in the breakthroughs' dialog. This can be achieved by setting the strategy as "visible to everyone" from privacy settings or by the user belonging to a team that was lined to a breakthrough.
The matrix below shows what each role can see and do in the Strategy-module. A detailed description of each role and how they are set can be found from the end of the article.
Limited access rights in the user interface
Limited access rights are visible as lock-icons in the UI. Users cannot interact with selections that have the lock icon on them:
![]()
If an organization has strategies that are set as visible to "participants only", they are completely hidden in strategy listings (e.g. in filters or strategy selection menus) for all the non-participant users.
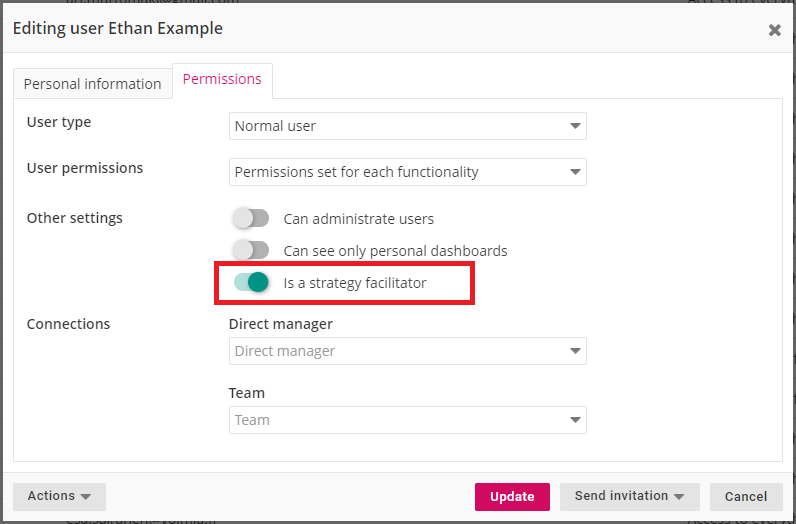
Strategy facilitator
Strategy facilitators can add, edit and delete any of the organization's strategies and their parts. They can also publish any strategy. Strategy facilitator status is activated from "Permissions" tab in user settings:
Strategy administrator and owner
Strategy administrators can edit the strategy and add, edit or delete its substrategies and any strategy parts. They can also publish the strategy or any of its substrategies. Administrator-status inherits from top to down in strategies, i.e. if a user is an administrator for a strategy, they are automatically administrators for any of its substrategies. Strategy administrators are defined in the strategy's settings along with the participants and privacy:
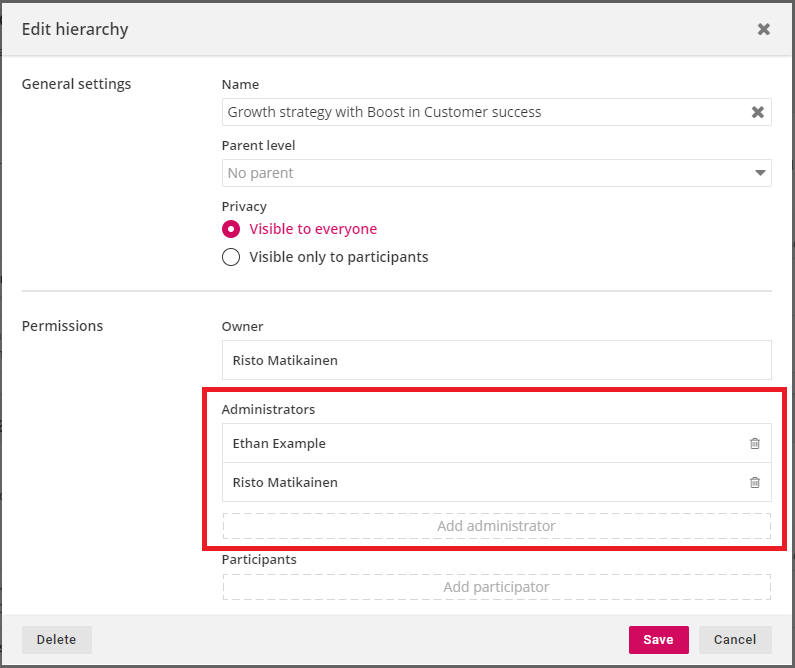
Strategy owners have the same access rights as the administrators. Users can become owners only by creating a strategy or substrategy.
Strategy participant
Strategy participants can add new substrategies and breakthroughs to strategies and edit or delete these, but they cannot edit or delete any strategy or their strategy parts that other users have added. However, they can publish the strategy and are added automatically as recipients for the summary of the publish. Strategy participants are defined in the strategy's settings below the strategy administrator (see previous picture above)
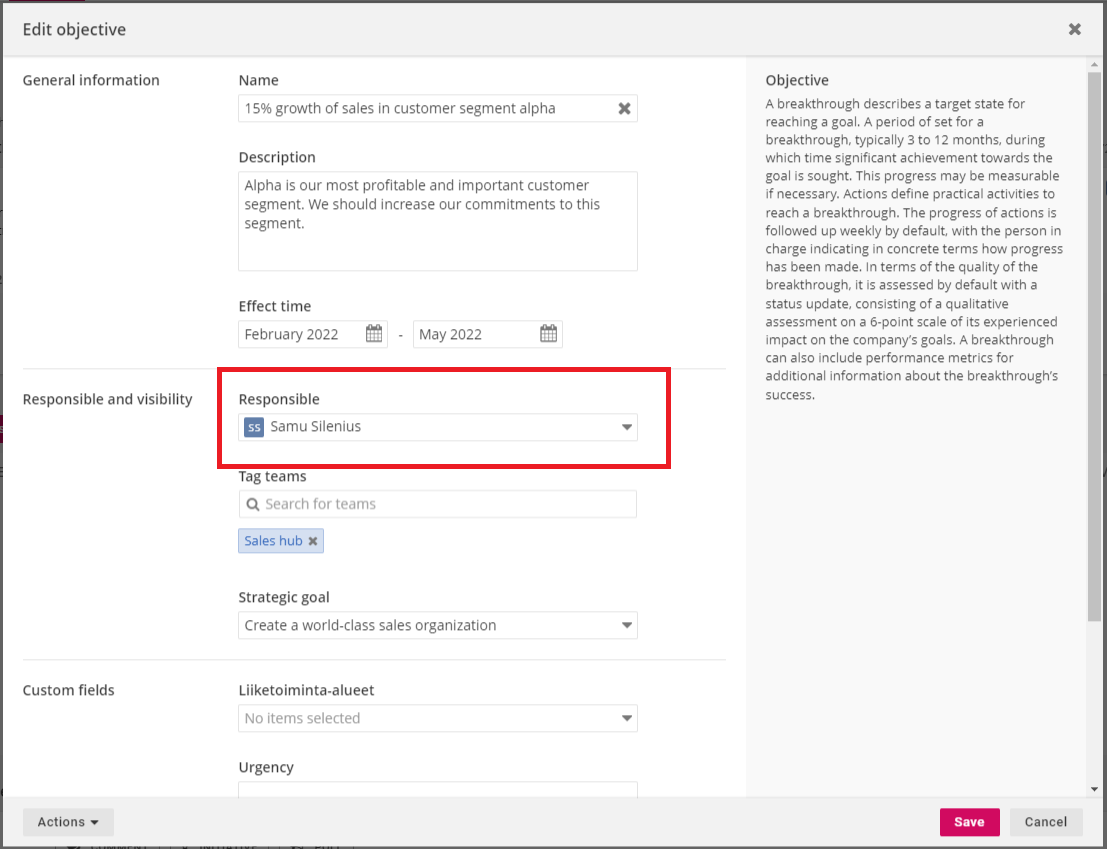
Breakthrough responsible
Breakthrough responsibles can edit their breakthrough and add, edit and delete actions that belong to it. In addition, they can see the other strategy parts. Breakthrough responsibles are defined in breakthrough settings:
Setting unknown user as responsible for draft breakthroughs
When a breakthrough is still in "draft" status, no user has to be defined as a breakthrough responsible. This is achieved by clicking the "X" at the right side of the responsible selection-field and this sets the responsible as "? Unknown user". This gives organizations flexibility for their strategic planning process as they can add breakthroughs without immediately assigning one of the users as a responsible:
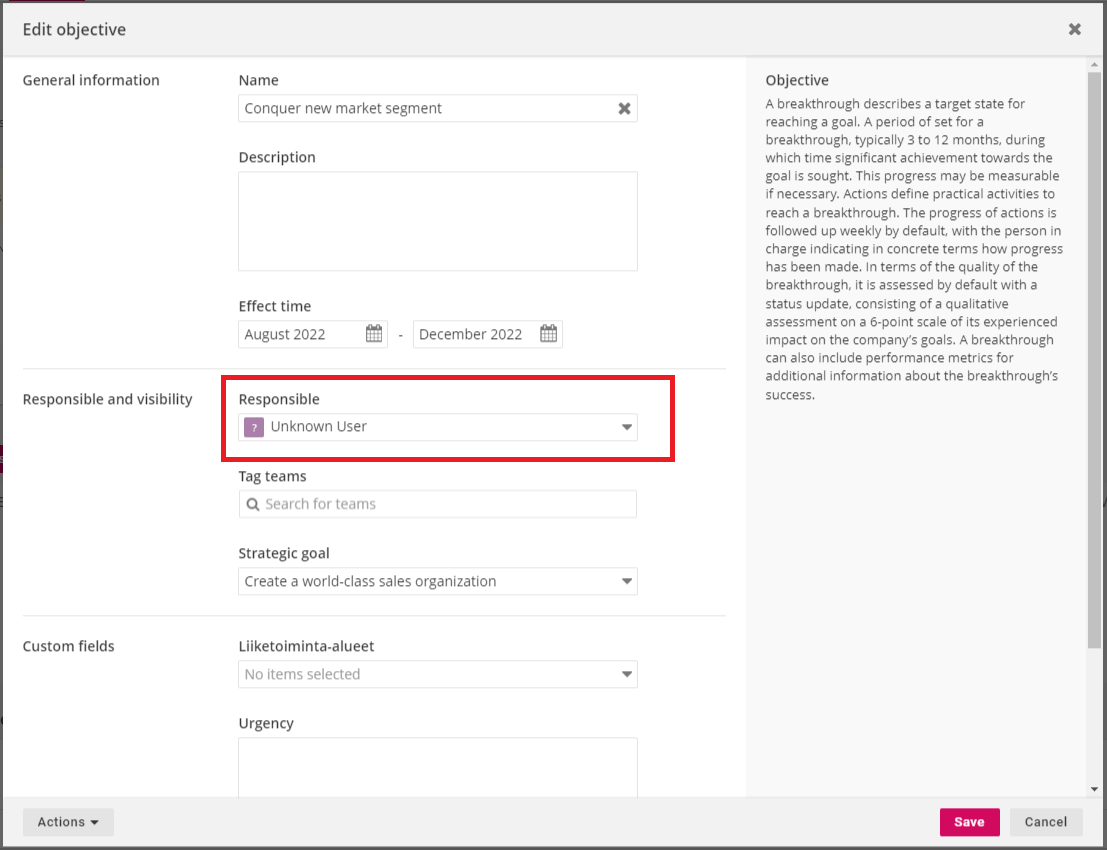
When the breakthrough is published, a responsible user has to be assigned to ensure that an individual will be responsible for the status updates.
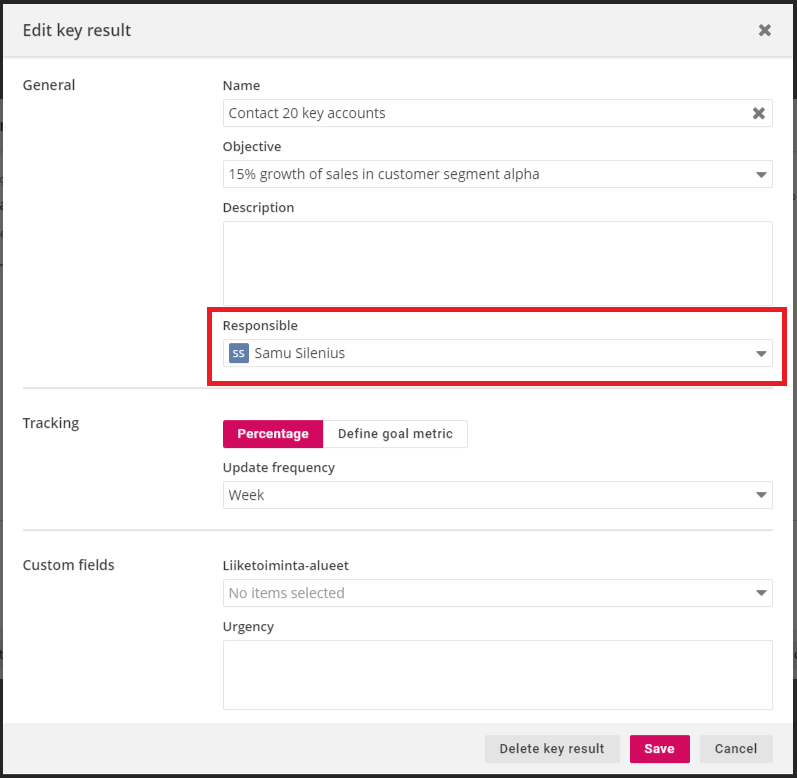
Action responsible
Action responsibles can edit their action, add other actions to the breakthrough as "drafts" and participate in breakthrough's dialog. They can also see the other strategy parts. Action responsibles are set in action settings:
A member of a team that is tagged to a breakthrough
Members of teams that are tagged to the breakthrough can add "draft" actions and participate in breakthrough's dialog. They can also see the other strategy parts. Tagged teams are added in breakthrough settings just below the breakthrough responsible-selection (see picture in "Breakthrough responsible"). Users are assigned to teams in the "Permissions" tab in user settings or in the Organization structure-mindmap.
Checking strategy access rights
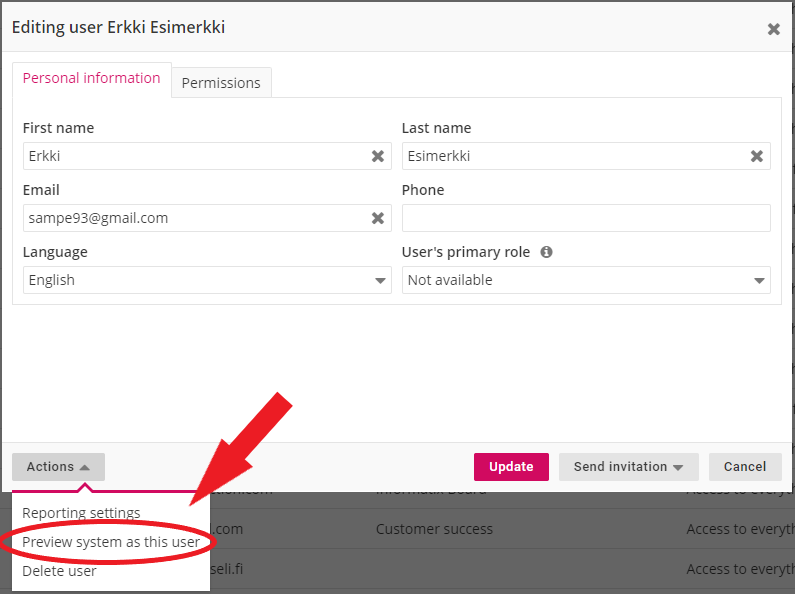
Because one organization can have multiple strategies and dozens of users with different roles, it can sometimes be hard to track what each user can see and do in the Strategy module. Luckily, strategy access rights can also be checked conveniently by using the "preview system as this user"-function that is activated from the user settings. The preview allows the user to see the service exactly as the selected user sees it and this can be used to test if their access rights are as intended: